In October 2020, it was revealed that the popular service Gravatar had been hacked, and the usernames and hashed email addresses were leaked. In May 2014, Bitly suffered from a data breach that caused the email addresses and hashed passwords of nearly 10 million users to be leaked. These are just some examples of data breaches. What can you do if your email address, your passwords, and your hashed passwords have been part of such breaches?
A very popular method to find out if your username, email address, or password has been part of a data breach is to make a search on https://haveibeenpwned.com/. There you can immediately find information about whether your phone number or your email address has been part of such breaches. It can also be interesting to do a search for your password at https://haveibeenpwned.com/Passwords.
I also use a service named Surfshark Alert, a part of my Surfshark subscription. I have registered some of my IP addresses there and if any of them is included in a newly reported data breach I will immediately receive a notification. You can also find a similar function in the password manager from NordVPN named NordPass.
Has your email address and password been leaked? What to do?
Have you checked the status of your email address? Has the address been part of any data breaches? The fact that your email address has been leaked might not be very dangerous in itself. But, was the email address combined with more information? Was the email address leaked together with a 100% readable password? If so, change your password as quickly as possible. Have you used the same email address and password on several platforms? You should change the password on every single password and get rid of the leaked password(s) as quickly as possible.
Are you registered at lots of websites? How can you remember each password if you use different passwords everywhere?
It isn’t a coincidence that password managers are very popular (and necessary). These will help you generate secure passwords and store them in a secure place. As a result, the only password you will need to remember is your very secure master password combined with your email address. The rest is the work of the password manager. There are lots of great password managers out there. Personally, I can warmly recommend NordPass and LastPass.
These password managers come with browser extensions and mobile applications. As a result, you will have all your passwords easily accessible whenever you need them.
But, what if you have received a warning that your password hash has been leaked? Is that dangerous? What does it mean that your password hash has been leaked?
My password hash has been leaked. Is it dangerous? What does it mean?
Maybe your password hasn’t been leaked, but your password hash has been leaked. What does that mean? Should you worry?
What is a password hash?
Many service providers add an extra layer of security as they store their user data. Instead of storing your password in normal words and letters, they encode it using different hashing technologies. Let us say that you register a new user at mynewwebsite.com with the following data.
- Email: [email protected].
- Password: 12345678
As the provider hashes this information it will be stored in their database like this.
- Email: [email protected] (if they would hash it with MD5, it would be: 4dec7aa05010e30721aa8714e9339a9e)
- Password: 25d55ad283aa400af464c76d713c07ad (MD5), 7c222fb2927d828af22f592134e8932480637c0d (SHA1)
Above you can see my password 12345678 encoded with the MD5 and the SHA1 hashing algorithm.
If someone would see this data and tried to log in with your account on mynewwebsite.com using the email address and the hash, it wouldn’t work. They would be unable to log in to your account. Does this mean that you don’t have to worry?
Do you have to worry if your password hash has been leaked?
There are problems here that you should be aware of. If you use the same hashing algorithm and encode the same password, the outcome hash will always be the same. What does this mean? If you use the same password that I do (12345678) and use the same hashing algorithm, you will get the same outcome (hash). Because of this, you will find databases connecting hashes with frequently used passwords.
If you go to https://crackstation.net/ and enter the two hashes above, you will see the following results.
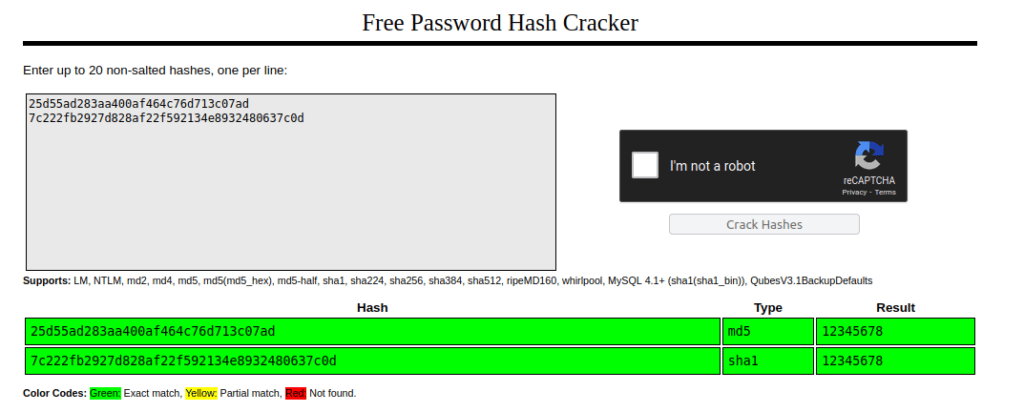
Do you see what I see? I simply added the hashes at the website above and it immediately showed me which type of algorithm was used and what the original password was. At first, the hash might seem very secure, but in reality, it doesn’t have to be. Has your password hash been part of a data breach? I recommend that you visit the site above and checked whether your hash has been exposed in so-called rainbow tables.
Some salt might give you extra protection!
As you can see above, a password hash might not protect you a lot (if the base password was a well-known password). Hackers will have plenty of computing power available, meaning that they can test your hash against millions of passwords quickly (using dictionaries and random letters and numbers), making it even scarier.
To protect us against such brute force attacks it has become normal to add salt to the hash. What does this mean?
In cryptography, a salt is random data that is used as an additional input to a one-way function that hashes data, a password or passphrase.
Wikipedia
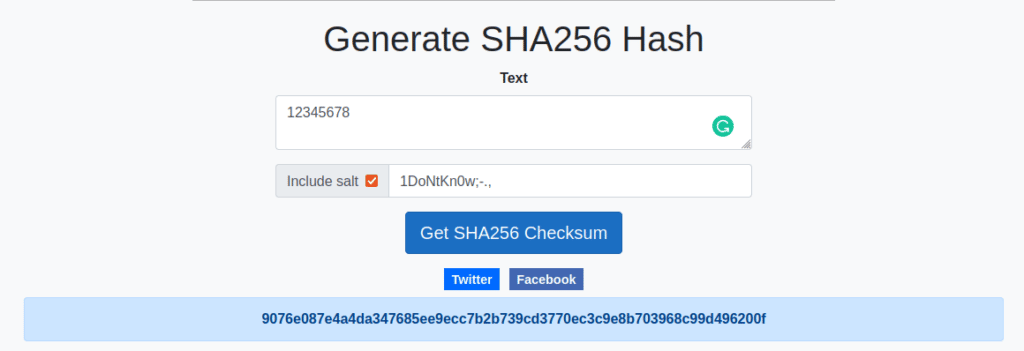
Salt is here additional data that is added to the hash. As a result, your password will no longer be dashed as 12345678, but you will get a bunch of other characters added to the password in addition. Below you can see an example of me encoding my password using the SHA256 algorithm, with and without salt.
- 12345678 (SHA256, without salt) = ef797c8118f02dfb649607dd5d3f8c7623048c9c063d532cc95c5ed7a898a64f
- 12345678 (SHA256, with salt 1DoNtKn0w;-.,) = 9076e087e4a4da347685ee9ecc7b2b739cd3770ec3c9e8b703968c99d496200f
As you can see, the hashes are completely different, and it will be way harder for anyone to decode the second hash due to the salt that is added to the hash. It is turning more and more normal to add salt to hashed passwords, but not everywhere.
No matter if a service adds salt to your password hash or not, you should always use secure passwords combining letters, numbers, and special characters, as that is the foundation of it all. Should one such password still be a part of a data breach, change it quickly. Since you use different passwords for all your accounts, you will still be safe!
I hope this article has managed to answer the questions you had before you came to read the article. If your password and/or your password hash have been part of data breaches, be careful and take the necessary steps to protect your accounts in the future.
If you have any further comments or questions, please use the comment field below.